Guide to Shodan Dorks and Cybersecurity Best Practices (2024)
Discover Shodan's powerful capabilities and dorks, revealing internet-exposed devices from webcams to critical infrastructure. Explore their security implications and how organizations can safeguard against cyber threats.
In the digital age, understanding the landscape of internet-connected devices is crucial for cybersecurity professionals, researchers, and tech enthusiasts. Shodan, often described as the search engine for the Internet of Things (IoT), offers unparalleled insight into the devices connected to the internet. Leveraging Shodan dorks — specialized search queries — can help identify vulnerabilities, gather data, and enhance security measures. This comprehensive guide will explore Shodan dorks, their applications, and best practices in cybersecurity for 2024.
Introduction to Shodan
Shodan is a search engine that scans the internet for connected devices. Unlike traditional search engines that index web content, Shodan indexes information about the devices themselves, including servers, routers, webcams, and more. This makes Shodan an invaluable tool for cybersecurity professionals looking to identify and mitigate potential security threats.
How Shodan Works
Shodan operates by continuously scanning the internet and collecting data on devices that are publicly accessible. It collects information such as:
- IP Address: The unique identifier for the device on the internet.
- Open Ports: The communication endpoints on the device.
- Services and Protocols: The applications and protocols running on the device.
- Banner Grabbing: The metadata about the service, including versions and configurations.
Shodan's data can reveal a lot about the security posture of a network, including potential vulnerabilities that could be exploited by attackers.
Understanding Shodan Dorks
Shodan dorks are specific search queries that help filter the vast amounts of data indexed by Shodan. These dorks can be used to find devices based on location, organization, operating system, and more. Here are some fundamental Shodan dorks and how they can be used:
Basic Shodan Filters
- city: Find devices in a particular city.
- Example:
city:"USA"
- Example:
- country: Locate devices in a specific country.
- Example:
country:"IN"
- Example:
- geo: Search for devices using geographical coordinates.
- Example:
geo:"56.913055,118.250862"
- Example:
- hostname: Find devices by hostname.
- Examples:
server:"gws" hostname:"google" hostname:example.com -hostname:subdomain.example.com hostname:example.com,example.org
- Examples:
- net: Find devices based on an IP address or CIDR range.
- Example:
net:210.214.0.0/16
- Example:
- org: Search for devices by organization.
- Examples:
org:microsoftororg:"United States Department"
- Examples:
- asn: Search by Autonomous System Number.
- Example:
asn:ASxxxx
- Example:
- os: Find devices based on their operating system.
- Examples:
os:"windows 7",os:"linux 3.x"
- Examples:
- port: Search for devices based on open ports.
- Examples:
proftpd port:21
- Examples:
Time-Based Filters
- before/after: Find devices before or after a given time.
- Example:
apache after:22/02/2009 before:14/3/2010
- Example:
SSL/TLS Certificates
- Self-signed certificates: Find devices with self-signed certificates.
- Example:
ssl.cert.issuer.cn:example.com
- Example:
- Expired certificates: Find devices with expired SSL/TLS certificates.
- Example:
ssl.cert.expired:true
- Example:
- Certificate subject: Search for devices by certificate subject.
- Example:
ssl.cert.subject.cn:example.com
- Example:
Advanced Shodan Queries
Advanced queries can pinpoint specific vulnerabilities and configurations. These include searches for industrial control systems, database servers, and network devices.
Industrial Control Systems
- Gas Station Pump Controllers:
"in-tank inventory" port:10001 - Traffic Light Controllers:
mikrotik streetlight - Automatic License Plate Readers:
P372 "ANPR enabled" - Voting Machines in the United States:
"voter system serial" country:US - Open ATM:
NCR Port:"161" - Telcos Running Cisco Lawful Intercept Wiretaps:
"Cisco IOS" "ADVIPSERVICESK9_LI-M"
Databases and Web Components
- MongoDB:
"product:MongoDB" mongodb port:27017 - MySQL:
"product:MySQL" mysql port:"3306" - Fully Open MongoDBs:
"MongoDB Server Information" "Set-Cookie: mongo-express=" "200 OK" "MongoDB Server Information" port:27017 -authentication - Kibana Dashboards without Authentication:
kibana content-length:217 - ElasticSearch:
port:9200 json port:"9200" all:elastic port:"9200" all:"elastic indices"
Remote Desktop and Network Infrastructure
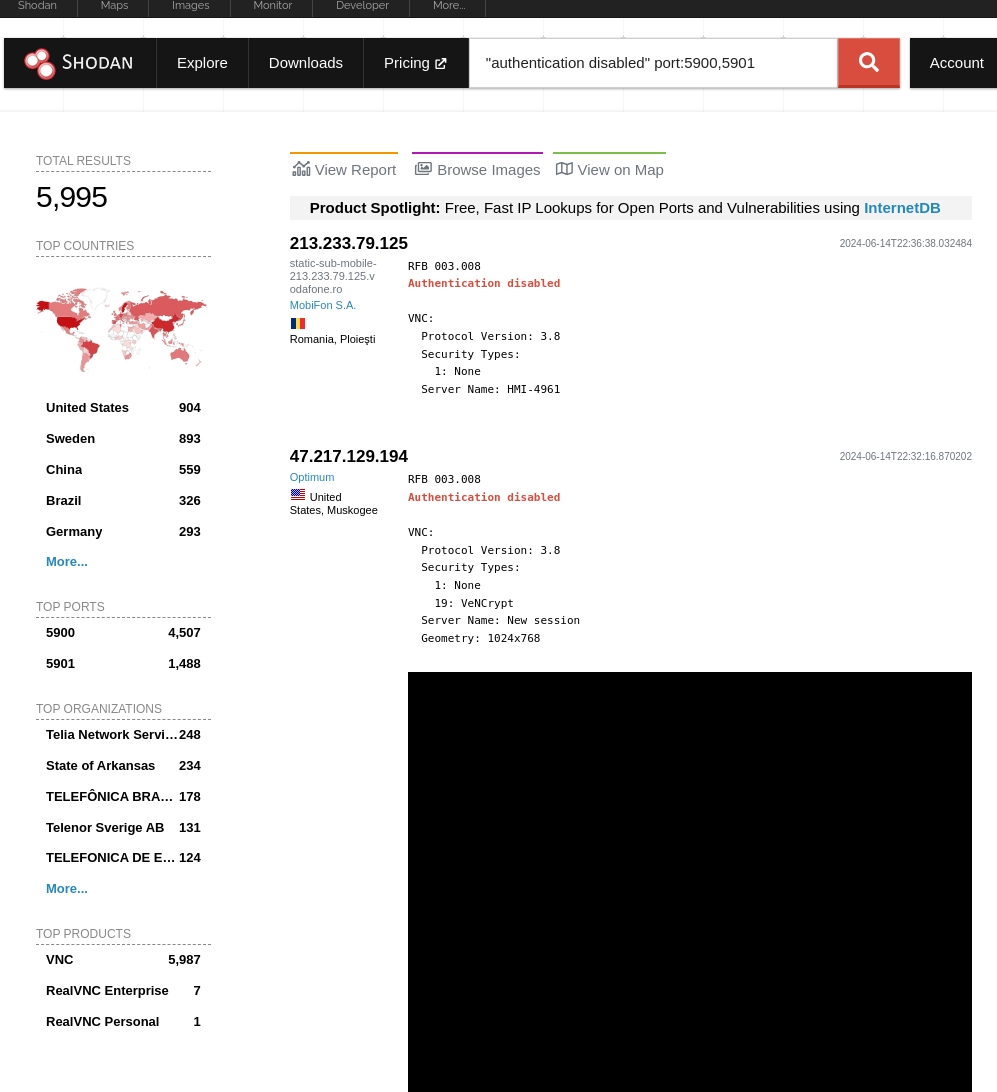
- Unprotected VNC:
"authentication disabled" port:5900,5901 - Windows RDP:
"\x03\x00\x00\x0b\x06\xd0\x00\x00\x124\x00" - CobaltStrike Servers:
product:"cobalt strike team server" product:"Cobalt Strike Beacon" ssl.cert.serial:146473198 - Redis Open Instances:
product:"Redis key-value store" - Docker APIs:
"Docker Containers:" port:2375 - Pi-hole Open DNS Servers:
"dnsmasq-pi-hole" "Recursion: enabled" - DNS Servers with Recursion:
"port:53" Recursion: Enabled - Telnet Access without Password:
"root@" port:23 -login -password -name -Session
Webcams and Home Devices
- Generic Camera Search:
title:camera - Webcams with Screenshots:
webcam has_screenshot:true - D-Link Webcams:
"d-Link Internet Camera, 200 OK" - Yawcams:
"Server: yawcam" "Mime-Type: text/html" - Security DVRs:
html:"DVR_H264 ActiveX" - HP Printers:
"Serial Number:" "Built:" "Server: HP HTTP" - Epson Printers:
"SERVER: EPSON_Linux UPnP" "200 OK"
Practical Applications of Shodan Dorks
Using Shodan dorks can provide insights into various devices and systems. Here are some practical applications:
Location-Based Searches
Find devices in specific geographical areas to assess regional cybersecurity landscapes:
- Example:
country:us city:chicago
Organizational Searches
Understand the technology stack and potential vulnerabilities of specific organizations:
- Example:
org:microsoft
Device and OS Identification
Identify devices running outdated or vulnerable operating systems:
- Example:
os:"windows 7"
Critical Infrastructure
Monitor critical infrastructure systems for security threats:
- Gas Station Pump Controllers:
"in-tank inventory" port:10001 - Traffic Light Controllers:
mikrotik streetlight
Database Security
Ensure databases are not exposed to the internet without proper authentication:
- Fully Open MongoDBs:
"MongoDB Server Information" "Set-Cookie: mongo-express=" "200 OK" "MongoDB Server Information" port:27017 -authentication
Case Studies
Case Study 1: Protecting Industrial Control Systems
A cybersecurity firm used Shodan to identify and secure vulnerable industrial control systems (ICS). By searching for specific ICS devices using queries like "in-tank inventory" port:10001, they discovered numerous gas station pump controllers exposed to the internet. The firm then worked with the gas stations to secure these systems, preventing potential cyberattacks.
Case Study 2: Securing Open Databases
A large corporation used Shodan to audit their database security. By searching for "product:MongoDB" mongodb port:27017, they found several MongoDB instances that were publicly accessible without authentication. The company promptly secured these databases, preventing potential data breaches.
Cybersecurity Best Practices
Leveraging Shodan effectively requires a solid foundation in cybersecurity best practices. Here are some recommendations to enhance your security posture:
Regularly Update and Patch Systems
Ensure all systems and devices are regularly updated to protect against known vulnerabilities. Patch management should be an integral part of your cybersecurity strategy.
Implement Strong Authentication Mechanisms
Use multi-factor authentication and strong, unique passwords to secure access to devices and systems. Avoid using default credentials, and regularly update passwords.
Monitor and Audit Network Traffic
Regularly monitor network traffic for unusual activity that could indicate a security breach. Use intrusion detection systems (IDS) and intrusion prevention systems (IPS) to enhance network security.
Use Encryption for Data Transmission
Encrypt data in transit and at rest to protect sensitive information from unauthorized access. Use protocols such as SSL/TLS for secure communication.
Conduct Regular Security Audits
Perform regular security audits and vulnerability assessments to identify and mitigate potential threats. Use tools like Shodan to continuously monitor your network's security posture.
Implement Network Segmentation
Segment your network to limit the spread of an attack. Use firewalls and access control lists (ACLs) to control traffic between different network segments.
Educate and Train Employees
Provide regular cybersecurity training to employees to raise awareness about potential threats and best practices. Educate them on the importance of following security protocols and reporting suspicious activity.
Conclusion
Shodan dorks provide a powerful way to explore the vast landscape of internet-connected devices. By mastering these filters and queries, you can enhance your cybersecurity efforts and conduct thorough research.
